This article is more than 1 year old
Adobe warns of attacks exploiting critical Flash flaw
Patch coming, but you'll have to wait
Adobe has promised to update its Flash media player to patch a critical vulnerability that is being exploited in targeted attacks to install malware on end user machines.
The attacks are being launched using emails that attach a Microsoft Word document that contains a booby-trapped Flash file, according to a blog post published on Monday by independent security researcher Mila Parkour. Clicking on the document causes Windows-based machines to install a backdoor known as Zolpiq, separate researchers from antivirus provider Kaspersky said.
“Given the interest on the list in China's Anti-Monopoly Law, the current issue of the ABA Antitrust Section's Antitrust Source may be of interest,” the email, which contains no spelling mistakes or glaring grammatical errors states. Copies of the message were sent as recently as Friday to unknown people, Parkour's post indicates.
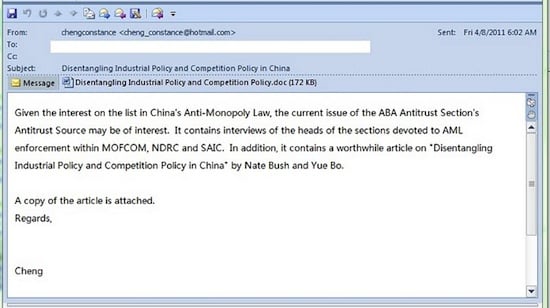
Copy of email exploiting critical Adobe Flash vulnerability
Just 1 of the 42 top antivirus products detected the threat, according to a VirusTotal analysis conducted over the weekend, and even that was a false positive for an unrelated piece of malware. Adobe officials said they're unaware of any exploits that directly target the vulnerability in its Flash or Reader applications.
Adobe didn't say when the fixes would arrive for Flash, but said it won't be able to fix the vulnerability in Reader for Windows until June 14. Reader for Linux and Solaris, and for phones running Google's Android operating system aren't vulnerable.
Word of the in-the-wild attacks comes one month after Adobe warned of similar attacks that targeted a separate Flash vulnerability. In both cases, the attackers embedded the malicious SWF file in a Microsoft Office document, presumably because a security sandbox recently added to Windows versions of the document viewer prevents the attackers from executing code on would-be victim's computers.
Those who have a legitimate need to embed Flash content in Word and Excel documents are almost certainly in the minority. With SWF exploits piggybacking on Office files for the second time in as many months, it's time for Microsoft to quickly figure out how to let users disable SWF content from all Office documents.
It's not clear if the attacks work against newer versions of Office, which come with security protections such as Address Space Layout Randomization designed to prevent the execution of malicious code. ®
